Sites often have simple black or dark-themed backgrounds and minimal design elements. Another sensible general rule to follow on the dark web is to not buy anything there. There are simply too many risks, such as honeypot sites set up by governments waiting for you to submit your info and fake marketplaces and scam sellers who won’t actually send you the items you buy. Take a look at your Tor Browser settings before you start your first dark web browsing session. It has a range of settings you can configure to help with security and privacy.
Can I Protect My Privacy Without Going Onto The Dark Web?
- GNUnet isn’t just a browser—it’s more of a platform for building decentralized networks.
- Browsers such as Google, Bing, DuckDuckGo act like virtual librarians, sorting and cataloging materials so they can be easily searched.
- That’s why at TecnetOne, we don’t just collect data—we use smart technology and expert analysts to separate what matters from what doesn’t.
- Understanding how to access the dark web is valuable for IT leaders, cybersecurity experts, and professionals who need to monitor hidden threats or preserve online privacy.
- Selling drugs or hiring a hitman to kill your ex will get you into trouble.
- Upon opening the Tor website, you will be presented with various download options for the operating systems that Tor supports, including Windows, macOS, Linux, and Android.
Although browsing the dark web is not illegal, it contains unsavory activities that can expose you to danger. Remember that any website engaging in illegal activities such as drug trafficking, weapons sales, hacking, and human trafficking violates international laws and, therefore, is illegal. The entry node encrypts your traffic and it bounces across several nodes in the Tor networks until it reaches the exit node. This node decrypts your traffic and it reaches the destination i.e. the website you want to visit. While accessing the dark web isn’t necessarily wrong or illegal, it’s important to know how to navigate this part of the internet safely.
The child pornography site Playpen is one of the famous scenarios that resulted from the dark web. The site had only been up and running for about seven months, but surprisingly, it gained over 215,000 users. By doing so, early signs of fraud can be detected in near-real time, such as new inquiries on your credit file, like new credit cards or bank loans.
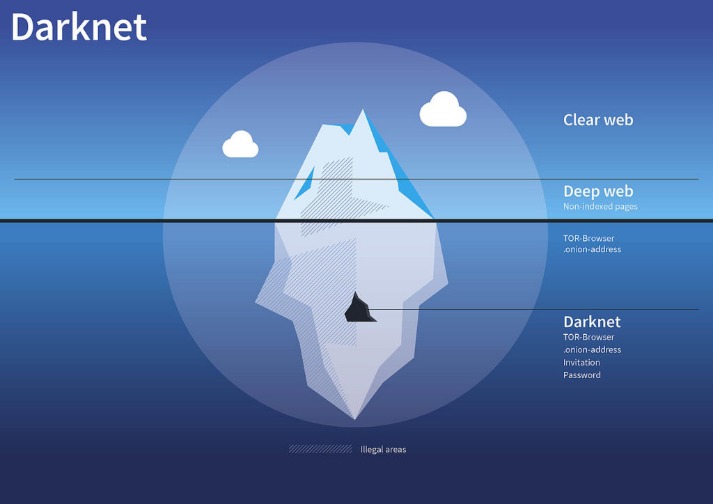
Mostly on the dark web, financial transactions happen via cryptocurrencies such as Bitcoin, making it possible for parties to do business anonymously. The open web makes up less than 4-5% of the internet, which is just the tip of the iceberg of the entire internet. Think of it as an iceberg, with only a tiny part visible above the surface. If you dig deeper, you’ll discover the mysterious world of the deep web and, for the brave ones, the foreboding dark web. The silver lining is that VPNs work on iPhones so you can mitigate the risk by connecting to one beforehand. The exit node can also be compromised but our experience has shown this happens extremely rarely.
How Do I Access Tor?
Cracking down on many illegal marketplaces on the dark web is the result of such monitoring. So, you risk being flagged or investigated for visiting certain sites, even without criminal intent. On the other hand, the deep web is the hidden part of the Internet that contains private or restricted content that is not indexed by search engines. Unlike the surface web, you can’t access deep web resources directly through a search engine; they require login credentials or special permissions. A 2014 study found that the most common type of content found on Tor, the most popular darknet, was child sexual abuse material. The dark web wasn’t the invention of a single individual but from efforts to build secure, anonymous communication.
Designed to be hidden from conventional search engines like Google or Bing, the dark web is a portion of the internet. Access to “.onion” domains and anonymous surfing made possible by specialised software like the Tor Browser allows entry only. A budget-friendly VPN service allowing users to access dark web safely anytime, anywhere, and on any number of devices they want.
Head over to our page on how to safely access the dark web for some top security tip. Most people have heard of the dark web and the illicit marketplaces available on it. Those marketplaces – and the stories surrounding them – can make the dark web seem like a hive of criminality. Unfortunately, it is true that guns, drugs, stolen passports (and many other illegal wares) do proliferate in those stores. As a result, there are plenty of reasons why the average person might choose never to access the dark web. As the digital environment evolves, so do the tactics employed by cybercriminals, law enforcement agencies, and privacy advocates.
FAQ: More About Onion Sites
The dark web hosts various types of illegal content, such as stolen data, child exploitation material, and prohibited items. As an average Internet user, you may accidentally stumble upon such content. Your access to illegal content, even if it is unintentional, can violate laws in many countries. Tor, short for The Onion Router, is a privacy-focused network that allows you to browse the Internet anonymously. It works by routing your encrypted traffic through multiple volunteer-operated servers, known as onion routers.
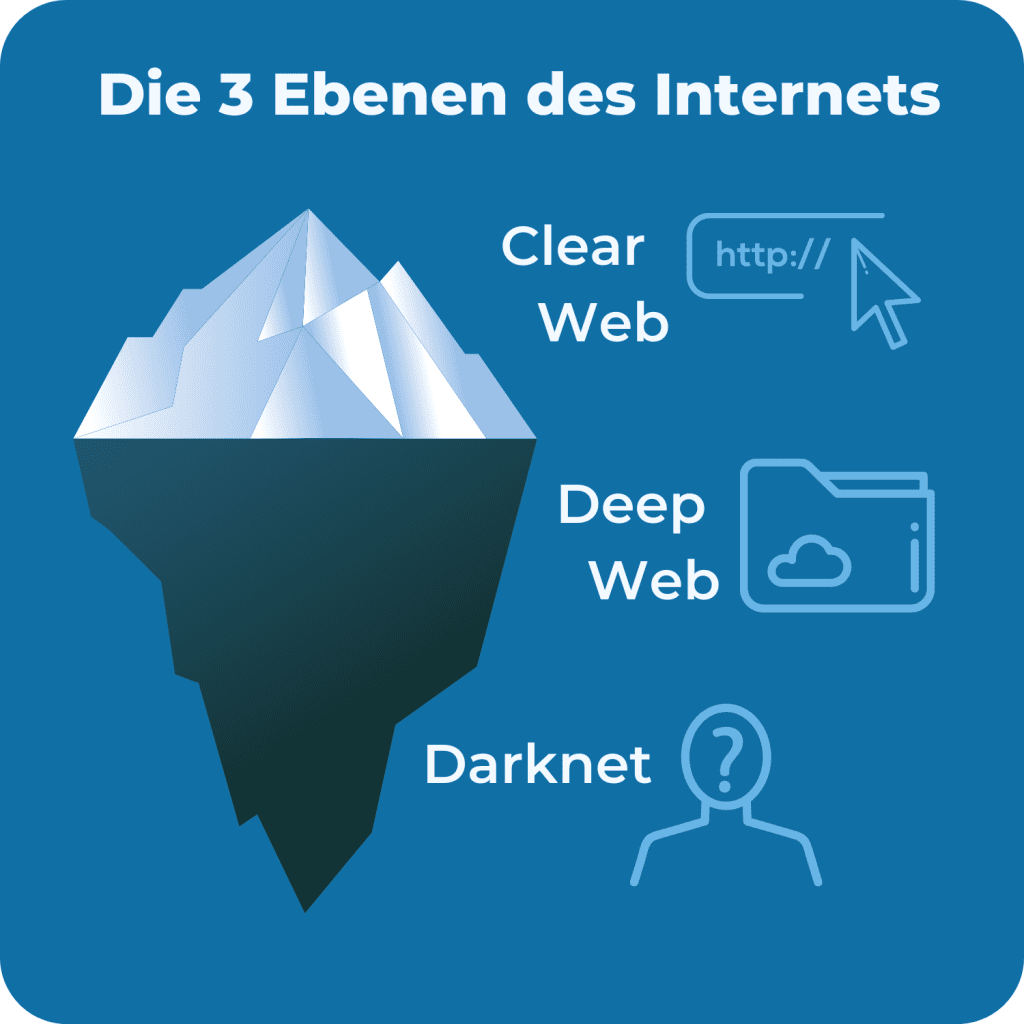
Information and data can be published and exchanged with the greatest possible anonymity on the so-called darknet, as PCWorld first noted in 2013. Deep down, the tip of the iceberg is where over 90% of the internet content is. As much as the dark web is supposed to promote free speech alongside bypassing censorship, many shady activities occur there.
Malware And Phishing
The place is as messy and chaotic as you would expect when everyone is anonymous, and a substantial minority are out to scam others. The dark web is a subset of the deep web that is intentionally hidden, requiring a specific browser—Tor—to access, as explained below. No one really knows the size of the dark web, but most estimates put it at around 5% of the total internet.
Your Data Can End Up Landing Anywhere
For example, DuckDuckGo is the most popular but often shows repetitive results and is sometimes unrelated to the question. Another Surfshark feature that stands out is the MultiHop mode. It will route your traffic through multiple servers instead of one, making tracking your data and activities even harder.
How To Browse The Dark Web Legally & Safely?
Below are some trustworthy starting points and authoritative references. By understanding the hazards you may face in the Dark Web and implementing the precautions outlined above, you’ll be better equipped to minimize your exposure to scams, malware, and identity risks. Remember that good judgment, ongoing education, and constant vigilance are your most powerful tools for maintaining a safe and private Dark Web experience. By familiarizing yourself with these networks and protocols, you gain a clearer understanding of the diverse strategies people use to stay hidden online.
Trusted Directories And Forums (stay Away From Hidden Wiki)
In fact, research performed at the University of Kent in 2015 revealed that 57% of the dark web hosts illicit material. That said, there are reasons some people use the dark web legitimately. In this guide, we will look at some of those reasons and explain how to access the dark web if you need to. Finally, you need to enter website addresses to access content on the dark web since you can’t browse by entering a search query as you can on the clear web.
The only difference is that it passes your traffic through random nodes before reaching the destination. This means your activities cannot be traced or your browser history exposed. Onion links have no regular domain names registered under the domain name registry. Instead, they are designed using a cryptographic key and can be accessed only through software like the Tor browser. As we stated earlier, the Hidden Wiki is an unreliable platform.
BBC Tor Mirror
This is also why it is essential to use strong passwords to protect any information stored on the deep web. By leveraging these resources and staying connected with professional communities, you can keep abreast of evolving technologies, threats, and best practices. By keeping an eye on these alternative platforms and trends, you gain a deeper understanding of how privacy, anonymity, and underground markets adapt to new technologies and challenges.
The Tor network allowed safe communication channels for political dissidents and American intelligence operatives around the world. Your information might be on the dark web if it was exposed in a data breach, sold, or stolen by hackers. To check, you can use dark web scanning or breach detection tools like Avast Hack Check or LifeLock Breach Detection to search for compromised data. If found, take immediate steps to secure your accounts and personal information. Some hackers offer ransomware as a service (RaaS), where cybercriminals can “rent” a strain of ransomware from its creator in exchange for a fee or a percentage of their ransom payments. Others sell software exploits that other cybercriminals can use to infect victims with malware and steal personal data.



