
One way to stay safe is to use a VPN while accessing the dark web, so be sure to check out my article on the best VPNs for the dark web. This means you can use your favorite browser instead of the Tor Browser and still benefit from being routed through the Onion Network. This ensures that your real IP address is hidden from the first Tor relay (it sees the IP address that your VPN provider supplies). Then the Tor anonymity network relays further obfuscate your true location, as the browser relays your browser traffic through several relay locations. That said, the Tor Browser and a VPN make an excellent team for protecting your online activities from prying eyes, and provide optimal online privacy protection. A secure VPN server slows down your browsing much less than the Tor Browser and also opens access to geo-blocked local content around the globe.
Are Onion Sites Dangerous?
From drug trafficking to arms deals to stolen data, the dark web provides a marketplace for many illegal goods and services. The dual nature of the dark web—as both a haven for privacy and a platform for crime—perfectly illustrates the complex ethical and security challenges it presents. Each relay peels off one layer of encryption, revealing the next relay’s address, until the final relay sends the request to the destination server. This multi-layered process makes it incredibly difficult to trace the user’s origin or the website’s physical location, ensuring a high degree of privacy and security. These websites are not accessible via normal web browsers like Chrome or Firefox, but require specialized software such as the Tor browser, which is designed to handle this unique routing protocol. Bearing in mind all the dangers, if you’re sure you’re willing to accept the risks, all you need to enter the dark web and access onion sites is an internet connection and Tor Browser software.
Tips To Stay Safe When Using The Dark Web
It’s also a good idea to set up a VPN for an extra layer of protection. Tor Metrics is a set of tools and data provided by the Tor Project that offers insights into the performance, usage, and activity of the Tor ecosystem and its nodes. Besides monitoring and improving the network, the data can be used to detect possible censorship or attacks. Due to the privacy-forward ethos of the Tor project, Tor Metrics stresses that the data it collects must not undermine the anonymity or security of the network. The dark web may be the Wild West of the internet — a place without rules, gatekeepers, or censorship — but there are still reasons to visit. Check out our list of the best dark web links and how to navigate onion and Tor sites safely.
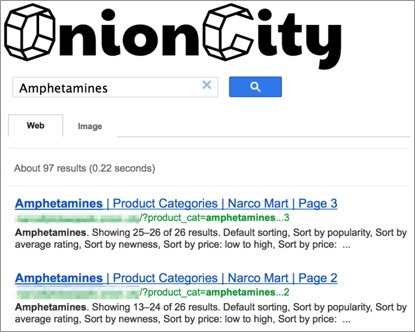
Unlike regular search engines, dark web search tools don’t always provide complete or up-to-date results. Some directories may list malicious links, while others are well-curated and focus on user safety. Knowing which ones to use is the first step in browsing the dark web responsibly. Anonymity of the dark web is one of the main draws for using onion sites, and most dark web links use a “.onion” domain. This is usually due to the sensitive nature of the businesses or services they offer. Onion sites may offer secure access to cryptocurrency wallets or anonymous email clients.
Tips To Stay Safe On The Dark Web
Lewis points to the “first contact problem”, when an attacker spots when someone moves from non-private tools to private ones, noting it’s been used to identify whistleblowers. Google doesn’t index these sites, but other search engines do, including DuckDuckGo, and there are lists — including one run by Muffett — so you can find what you’re looking for. If you are still unable to connect to the onion service after verifying the address, please try again later. There may be a temporary connection issue, or the site operators may have allowed it to go offline without warning. You can also test if you are able to access other onion services by connecting to DuckDuckGo’s Onion Service.
How To Safely Access The Dark Web With Tor — Step-by-Step Guide (
Furthermore, it’s critical to understand that Whonix is not a stand-alone browser. It is a component of Whonix, an operating system that functions as a whole inside a virtual computer. It includes all the essential productivity software, including MS Word and an email client.
- This prevents tracking and fingerprinting, because Tor browser isolates each website you visit, meaning that third-party trackers and ad networks can’t follow you around.
- This information can be used to target ads and monitor your internet usage.
- However, not Evil is not a repository for illegal services and illegal material.
- Another private cryptocurrency you’ll find being used is Monero, which prides itself on being untraceable.
How Do I Access Onion Sites?
- These sites are only accessible over the Tor network and are commonly used for privacy and anonymity.
- It’s a wallet, explorer service, not a dark web marketplace itself, but still a helpful resource.
- Also, try its services risk-free with the 30-day money-back guarantee.
- If you exercise due caution and use a combination of the Tor browser and common sense in which sites you access on the dark web, yes, the dark web is safe to use.
- It is designed to ensure user anonymity while offering access to a diverse array of information available on the dark web.
You will find all the necessary .onion links to access any content or service on the dark web. Ahmia is a dark web search engine designed to index and search tor websites. This traditional search engine is also compatible with the dark web and can help you find dark web websites. ProPublica was the first online publication to win a Pulitzer prize. They were also the first to host a .onion site to make their content accessible to everyone everywhere, regardless of censorship or anti-journalist laws in certain countries. SecureDrop is a really awesome Tor service that can be used to share information without revealing your identity.
How Much Does It Cost To Use Tor Browser?
Download the Linux version from torproject.org, extract the file, and run the start-tor-browser script. Accessing the Dark Web using the Tor Browser is not just about exploring hidden parts of the internet—it’s about understanding privacy and cybersecurity in the modern world. Cybersecurity Student → Conducts research on privacy tools → Accesses ethical hacking forums (legal) using Tor. This blog offers a complete guide on how to access the Dark Web using the Tor Browser, along with step-by-step instructions, security tips, legal warnings, and real-world examples. While many dark web websites, like the former black market website Silk Road, are used to facilitate criminal activity, there are also plenty of legitimate dark web websites.
How To Access The Dark Web Using Tor

This allows you not only to visit sites with the added privacy provided by the Tor network, but also search the web as privately as possible from inside the Tor browser. Just remember that this is a Dark Web resource, which means that much of the content is likely in breach of copyright. That said, it is one of the most famous and popular Dark Web sites, and it does have legitimate uses. For instance, in the UK, any book older than 70 years old (past the date of the author’s death) is no longer subject to copyright restrictions. This means you can safely download older manuscripts and other public domain works. The dark web and the deep web are often used interchangeably, but they’re two distinct concepts.
In “safer” mode, JavaScript is disabled on HTTP sites, some fonts are disabled, and all audio and video won’t run automatically, you’ll have to click to play. Slide up to the “safest” level, and as well as those settings, JavaScript is disabled on all sites. That’s a trick question, because there isn’t even a good free VPN, much less a best VPN. Freebie VPNs will track their users’ online usage, as they make money by selling this tracking info to advertisers and other nosy parties.
Words Of Caution When Using Dark Web Sites
The topics you can find vary from literature, programming, science, and….artistic photography. Bear in mind that downloading materials from this site may put you in violation of local copyright laws, so exercise caution should you decide to do so. Not Evil is a reflection of what the community is looking for and what the community reports as abusive or inappropriate content.
This network of over 6,000 relays hides your location, thus protecting you from online surveillance and third-party tracking by your websites. Your activities on the dark web are not entirely shielded from tracking, and relying solely on anonymity can lead to a false sense of security. The dark web draws not only serious cyber criminals but also law enforcement agents aiming to catch them.



