Darren Guccione is the CEO and co-founder of Keeper Security, the world’s most popular password manager and secure digital vault. Keeper is the first and only password management application to be preloaded with mobile operators and device manufacturers including, AT&T, Orange, America Movil and HTC. Keeper has millions of consumer customers and the business solution protects thousands of organizations worldwide. Most e-commerce providers offer some kind of escrow service that keeps customer funds on hold until the product has been delivered. However, in the event of a dispute don’t expect service with a smile.
What Is The Dark Web? Here’s How To Access It Safely (and What You’ll Find)
If you need to access dark web resources, these are the steps you need to take. The dark web, however, requires special software to access, as explained below. Here’s everything you need to know about this other internet, as well as how to access it. The area of the internet we access daily is known as the clear or surface web. The internet opened the door to a realm of possibilities that permanently changed the business landscape and our personal lives.

How To Access The Dark Web On Phone
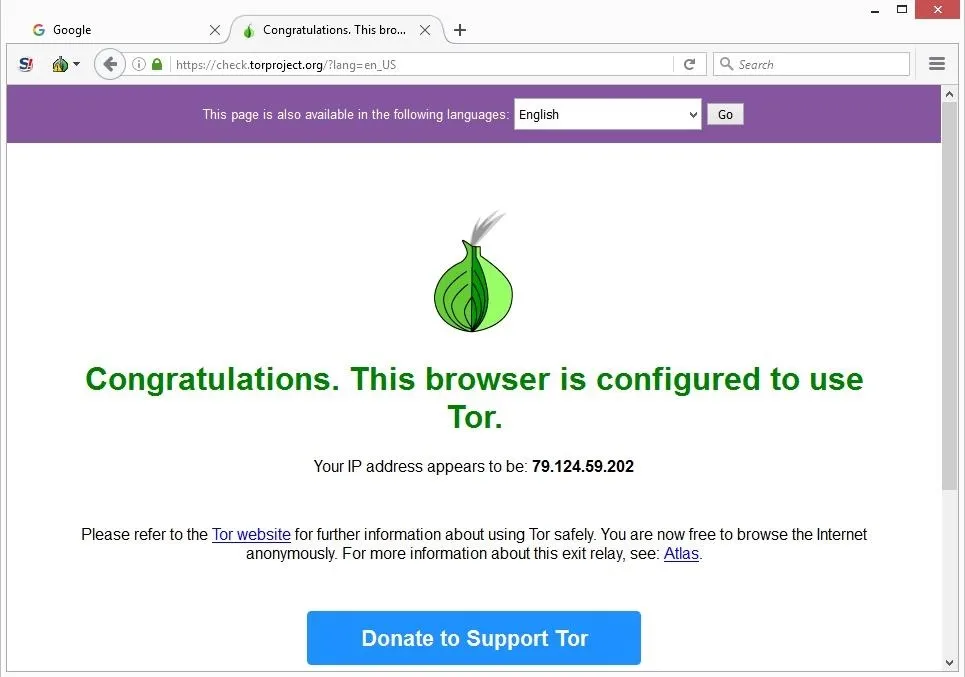
These servers, numbering in the thousands, are operated by volunteers worldwide. Using NordVPN or even ExpressVPN or PIA seems to be beneficial for many users. Such providers offer strong encryption and don’t store logs, ensuring all online footsteps are completely masked. Above all, it’s vital to go on the dark web carefully and sensically.
Cryptocurrencies And Financial Anonymity
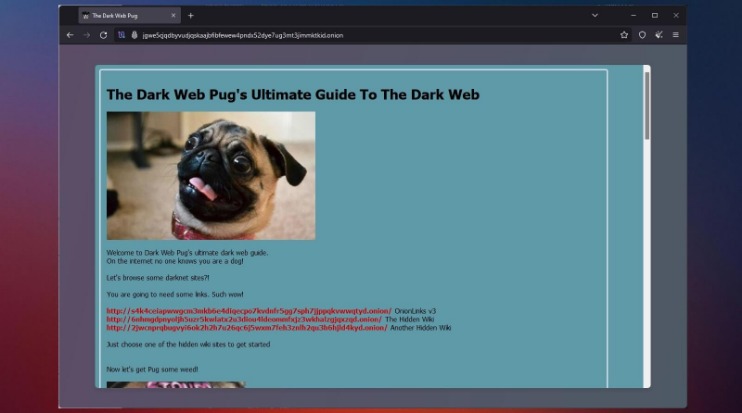
Deep web content includes academic research papers, court documents, or medical records. For example, when you sign in to your healthcare provider’s portal to view test results or request prescription refills, you’re accessing the deep web. The dark web — aka, the deep web — is the second layer of the internet, which is not indexed by search engines. Websites and pages in the deep web might include password-protected content, private forums, and personalized resources. When accessing the dark web, the first step is to install a dark web-friendly browser on your computer. Unlike traditional browsers, this will route your internet traffic through an anonymizing network and mask your IP address.
Instead, they are designed using a cryptographic key and can be accessed only through software like the Tor browser. As we stated earlier, the Hidden Wiki is an unreliable platform. This is the best place to get short and reliable links to an unalterable record of any webpage across government and corporate websites. Formerly known as Archive.is, it is one of the best onion sites on the dark web. It aims to preserve the internet’s scientific and cultural heritage.
While you can visit the obscure part of the internet without a VPN, it’s better to go with one. Here are our favorite choices that work well and support Tor Over VPN perfectly. If you don’t know where to start, you can use The Hidden Wiki to find a few dark web domains. Simply copy the URL of the site you want to visit, press Enter, and you’re all set. The button above leads you to its website where you can claim an exclusive 70% discount for the 2-year plan.
How To Access The Dark Web Or Deep Web Using Tor
Dark web search engines and forums like Reddit can help you find reliable dark websites, and you’ll need to use a dark web browser to visit them. The quickest way to access the dark web is to download and install Tor Browser, which will route your traffic through the Tor network and let you access the dark web. On Tor, you can type in any URL you’d like to visit, including .onion links on the dark web. Unlike typical web browsers, Tor Browser uses onion routing, which encrypts and routes traffic through multiple servers around the world to hide your IP address and provide private browsing. In addition, all domains on the Tor network end with the top-level domain .onion (instead of .com). The many layers of an onion represent the multiple layers of encryption in the Tor network.

WANT TO TRY THE TOP TOR VPN RISK FREE?
Fake sites are everywhere, and even a one-character difference in the URL can land you on a phishing page. Underneath it are deeper layers that aren’t visible through normal browsing. In today’s ever-evolving digital landscape, traditional perimeter-based security models are no lon… Ever noticed your Android device slowing down, apps glitching, or storage space mysteriously vanishi…
You will never know when you stumble upon illegal materials, inadvertently download malicious software, or expose yourself to identity theft. But if you must visit the dark web for ethical reasons, here are some safety precautions. Unlike other search engines, it does not collect or share web activities and personal data of users. Dark web encryption allows website owners and users to stay completely anonymous during their engagement. Dark web browsing is not as simple as regular web surfing, but there are some tools you can use to chart your journey.
While it’s generally safe to use, dark web activity can be detected at the entry and exit nodes of the Tor network. The primary purpose of accessing the dark web is anonymous browsing for activists and whistleblowers, but some people misuse this anonymity for illegal reasons. It is where the dark web becomes dangerous, and with no regulations, it becomes riskier to access without using a protective tool. The cybercriminals are scattered like landmines all around the dark web. Also, ISPs and government agencies monitor your network and track down IP addresses used to access the dark web. But just like when you’re online normally, the risks increase depending on what you do while visiting dark web websites.
Essential Safety Tips To Minimize Risks
Deep down, the tip of the iceberg is where over 90% of the internet content is. As much as the dark web is supposed to promote free speech alongside bypassing censorship, many shady activities occur there. Removing your sensitive personal information from the dark web once it has been exposed is virtually impossible. This (practically) irreversible process highlights the importance of taking preventive measures by utilizing a service that monitors your data for potential breaches.
To access the dark web, you’ll need a specific set of tools – more about that later in the step-by-step section. The invisible web is made up of data and information that is not indexed and cannot be searched for by using traditional search engines. It includes media and archives which cannot be crawled and indexed with current search engine technology. Instead, download Tor, the most secure and user-friendly option for accessing .onion sites. Despite some skepticism about its origins and privacy due to its military development, Tor remains the preferred choice for safe dark web navigation.
Step 1: Download Hyphanet

Depending on the device you’re using, there are 2 browsers you need to access the dark web on your phone. On Android, you need the Tor Browser, and on iPhone, you need the Onion Browser. Keep your personal details secure by using aliases and anonymous email accounts when creating dark web accounts. Using secure, anonymous tools helps protect your identity from potential threats on the dark web.
Each of these options offers unique privacy features, with Whonix and Qubes for higher security setups, and Kodachi and Liberté for portability. Choose a VPN known for strong encryption, a no-logs policy, and compatibility with various devices. This guide will teach you how to install the Tor Browser in Windows easily so you can access the Dark Web or browse the web anonymously. The same general process applies to other operating systems, as Tor is also available for Mac and Linux. While difficult, tracking is possible if security measures are misconfigured or if users reveal personal information.
The dark web wasn’t the invention of a single individual but from efforts to build secure, anonymous communication. Its foundation is the Onion Router (Tor) project, developed in the 1990s with funding from the U.S. Naval Research Laboratory to protect sensitive government communications. Later released as open-source, Tor became accessible to the public, enabling anonymous browsing for activists, journalists, and everyday users—while also giving rise to today’s dark web. There is a significant risk that the government can target you for visiting a dark website, as many Tor-based sites have been taken over by police authorities worldwide. Even if a person does not make any purchases on illegal marketplaces like the Silk Road, custom software used by law officials can analyze activity and identify user identities.
- There are reports of illegal services on the dark web, ranging from paid assassinations to the trafficking of sex and weapons.
- Read our posting guidelinese to learn what content is prohibited.
- While some threats on the dark web are well-known, others may use its notorious reputation to trick users into paying large sums of money.
- The “onion routing” technology underpinning the dark web was developed by researchers at the U.S.
- Supreme Court will allow the FBI to search and seize any computer that’s using the Tor browser or VPN.
- By familiarizing yourself with these networks and protocols, you gain a clearer understanding of the diverse strategies people use to stay hidden online.
The surface web (often referred to as the “visible web”) is the portion of the web available to the general public and indexed in the standard web search engines such as Google, Bing, and Yahoo. Always remember that the dark web is a people-centric community. So, it’s only natural to find ways to keep in touch with your darknet buddies and/or customers.



