
Also, you need to use a privacy-focused browser such as the Tor network to connect via nodes and proxy servers, which are more secure and aim to anonymize traffic requests. The Tor browser is able to access the special domain names, with the suffix .onion, used in the dark web. You need special tools to access the dark web, and the Tor Browser is the safest and most popular one. Make sure you download the Browser from the official website (torproject.org).

Step 5: Exit Safely
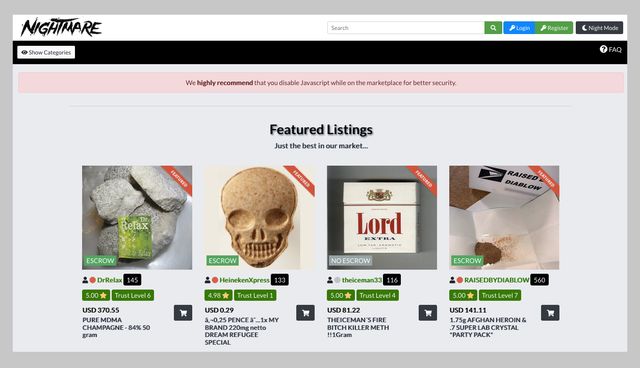
Here’s a look at several of the illegal items you can buy — with prices — courtesy of Privacy Affairs’s Dark Web Price Index 2023. While some reports of dark web murder-to-order are overblown, it is possible to commission acts of cybercrime on the dark web. These range from phishing campaigns to DDoS (distributed denial of service) attacks, which can take down entire servers and websites. To use the dark web safely, use as many privacy-enhancing tools or programs as you can, and do not identify yourself in any way to anyone for any reason.
Popular Dark Web Search Engines And Sites
You can use the VPN rated #1 for the dark web with no restrictions for a month—great if you want to try this no-log provider’s Onion over VPN servers for yourself. The easiest way to access Tor is through a special browser known as the Tor Browser. You might want to hide your Tor Browser download using a VPN and your existing browser’s private/incognito mode. Have you ever searched for a file you know exists but just can’t find?
It was created in 1999 as a secure communication platform for people and groups working on liberatory social change. The platform is protected from government interference and malicious attacks to protect the user. In addition, it ensures that no record of communication is stored. Unlike other search engines, it does not collect or share web activities and personal data of users. The dark web — aka, the deep web — is the second layer of the internet, which is not indexed by search engines.
Quick Comparison: Best Anonymous Dark Net Browsers
Even if you’re only attempting to visit legitimate sites, one wrong click could expose you to content you would rather not see. To minimize the risk, research and verify sites before visiting them. Given the prevalence of malware across the dark web, it’s vital to have antivirus software installed and active on your device when accessing it. Firstly, it could jeopardize your anonymity if you submit any kind of personal information during a dark web browsing session. Secondly, there are many malicious, fake, and phishing sites on the dark web, which might look like sites you trust but are actually designed to steal your data. The websites and online platforms that you find via your search engine are actually only a small part of the internet.
Onion Links: How To Access Them
We’ve compiled a detailed guide to help you explore the Top Darknet Markets. Discover the most trusted platforms like Anubis Market, and more, complete with their unique features and security measures. The silver lining is that VPNs work on iPhones so you can mitigate the risk by connecting to one beforehand. We’ve clarified how to go on the dark web anonymously with the help of a VPN. A VPN is a confusing factor for many because there are two ways to use it with Tor.
Detailed Steps To Access The Dark Web Using Tor
By some estimates, well over half of dark web content is illegal. This can include illicit marketplaces, drugs, cybercrime and hacking groups, and extremist, violent platforms. By following these straightforward steps, you significantly reduce the risk of exposure, protect your digital identity, and ensure a secure and anonymous browsing experience on the Dark Web. Yes, but for .onion sites, you’ll need search engines designed for the dark web like DuckDuckGo’s .onion version. Lokinet is easier to set up than I2P, and it may run faster than Tor in some cases, especially when visiting regular websites through its secure network.

How To Access The Dark Web Or Deep Web Using Tor

When using Tor, your traffic will never reach its intended destination directly, as it would on surface web browsers. Instead, it is funneled through different ‘nodes’ – other user’s computers – before coming out the other side. These computers are all owned by volunteers, passionate about privacy and happy to offer up their device to help others. Traffic is relayed through three nodes each time it passes through the Tor network. Although the dark web represents a small fraction of the totality of the deep web, it has attracted perpetual media attention over the last few years.
The dark web wasn’t the invention of a single individual but from efforts to build secure, anonymous communication. Its foundation is the Onion Router (Tor) project, developed in the 1990s with funding from the U.S. Naval Research Laboratory to protect sensitive government communications. Later released as open-source, Tor became accessible to the public, enabling anonymous browsing for activists, journalists, and everyday users—while also giving rise to today’s dark web. The dark web also helps individuals communicate about or sell illegal items such as weapons, drugs, malware, etc. Many people see hacked information and stolen card data being sold on the dark web.
- Though it’s still helpful, a static list isn’t enough (we try to keep our own, the one above, up-to-date, though).
- Many dark net sites do not undertake the necessary measures to protect users like most websites on the surface web.
- The deep web is every part of the internet that is not indexed by search engines, like private messages from your social media or your online banking portal.
- Although it’s not inherently illegal to access the Dark Web, remember that certain sites and activities may be.
- If you’re unsure about a link, do some research or ask trusted sources within dark web communities.
- The “Dark Web” often conjures up images of hidden marketplaces, illicit trades, and shadowy figures lurking in the digital underworld.
While it might appear tempting to venture into the dark web, it’s crucial to understand that the risks here are far more severe compared to the deep web. Therefore, if you do decide to explore it, exercise extreme caution. Everything you find on the dark web is not necessarily illegal. As listed above in our article, even respected organizations like the BBC and ProPublica have a version of their site on the dark web.
On Tor, you can type in any URL you’d like to visit, including .onion links on the dark web. Unlike typical web browsers, Tor Browser uses onion routing, which encrypts and routes traffic through multiple servers around the world to hide your IP address and provide private browsing. In addition, all domains on the Tor network end with the top-level domain .onion (instead of .com). The many layers of an onion represent the multiple layers of encryption in the Tor network. When accessing the dark web, the first step is to install a dark web-friendly browser on your computer.
How To Safely Access The Dark Web
The hidden nature of the dark web has earned it the nicknames black web and underground internet. However, these names likely conjure up a scarier conception than the real definition of the dark web. Upgrade your lifestyleDigital Trends helps readers keep tabs on the fast-paced world of tech with all the latest news, fun product reviews, insightful editorials, and one-of-a-kind sneak peeks. It offers outstanding privacy features and is currently available at a discounted rate. Second, shutting down or controlling access to the dark web would be a huge undertaking and could have unintended consequences. Finally, many people consider the dark web a necessary tool for privacy and freedom of speech.



