The power and integrity of OFAC sanctions derive not only from OFAC’s ability to designate and add...
wpadmin
JoyInc is believed to have been operating since at least 2018 and is one of the most...
In contrast to the ROK — where dealers appear to be largely Korean nationals — the dead...
The agency posted video is from a take-down in 2019, called Operation SaboTOR— a play on TOR,...
This came a day after Punjab Police seized a huge amount of drugs in a major operation...
It is illegal, and there are risks involved, including the risk of being caught by law enforcement...
Search no further than regulatory-compliant security cameras the steady alternative for making sure legal and regulatory compliance....
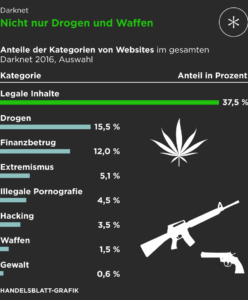
While the deep and dark web serve legitimate purposes, they also facilitate illegal activities and create difficulties...
There are often copious amounts of how-to articles, software exploits, and hacked credentials for sale. Not every...
Others are looking for stolen data, hacking services, or even banned books and political content. Some are...