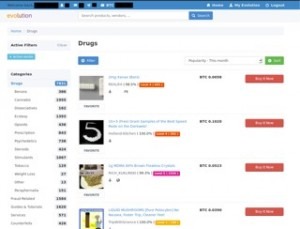
Its 9,000+ users and 700+ vendors focus on drug trades with strong escrow security. The growing popularity...
Uncategorized
Be warned, engaged in criminal activity can lead to you being arrested and prosecuted which can lead...
Never send coins directly from an exchange, and avoid storing funds in market-hosted wallets. By controlling your...
By aggregating verified links and providing up-to-date information, these lists reduce the time users spend searching for...
You won’t find any “hidden” stories here—it’s the same content as the normal web edition—but users in...
Due to its extensive inventory and reputation for reliability, Brian’s Club has maintained a significant presence on...
The evolution of darknet markets in 2025 has significantly enhanced the security and reliability of drug trade,...
However, it’s important to note that participating in these subreddits can be risky, as the dark web...
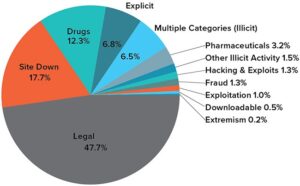
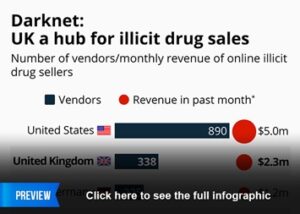
Since all activity on the dark web is anonymous by default, it is definitely where the murkiest...
Suddenly, anyone could share files directly without going through a middleman. This culture of direct exchange hinted...