The chart below shows this counterparty decline, as well as a drop in crypto flows across the fraud shop ecosystem. Fraud shops are services found mainly on the dark web that sell stolen data and personally identifiable information (PII), which cybercriminals use for scams, identity theft, and ransomware attacks. In 2024, fraud shop inflows declined by 50% YoY, a sharp downturn from the last three years. Deposits span from the hundreds to the tens of thousands of dollars, and the average deposit amount in 2024 was over $2,000. In 2024, however, many vendors of reagents and precursors have turned to criminal forums to advertise their product offerings, or have delisted (at least publicly) chemicals related to fentanyl synthesis. This could be in response to increasing pressure from the United States and China, and the crackdown on the websites selling these products.
How Darknet Market Lists Enhance Secure Drug Trade
This system fosters a competitive environment where vendors strive to maintain high standards, resulting in better quality products and services. Additionally, the wide range of available products caters to diverse preferences, making these markets a one-stop solution for users. In 2025, the darknet continues to serve as a hub for secure and efficient drug trade, with platforms evolving to meet user demands for privacy and reliability. The integration of advanced encryption technologies and decentralized systems ensures that transactions remain confidential, while user feedback mechanisms enhance trust among participants.
Will Law Enforcement Continue Targeting The Largest DNMs?
Changing the Tor browser settings can further boost your security levels on the dark web shops. For instance, you can choose the preferred security levels for enhanced protection. The security level is set to ‘Standard’ by default, but you can change it to the ‘safest’ and enjoy more security while accessing the dark web.

The Best Dark Web Markets To Consider In 2025
Implementing AI-powered fraud detection, enhancing oversight, and promoting responsible adoption will help build a more transparent and resilient crypto ecosystem. Cryptocurrency fraud has seen a significant rise in recent years, with various schemes exploiting the digital nature of cryptocurrencies. This section explores Ponzi and pyramid schemes, ICO scams, rug pulls, and phishing attacks, as well as cryptojacking, fake wallets, and fraudulent exchanges. Criminals employ layering and structuring methods to conceal their illicit Bitcoin transactions, which are hard to track and regulate. By breaking large sums into smaller transfers and leveraging multiple exchanges, they evade regulatory scrutiny. These methods exploit gaps in compliance frameworks, complicating efforts to track and prevent financial crimes.
Signs Of Trouble Had Already Starting Appearing In June
Abacus Market, the largest Western darknet marketplace supporting Bitcoin payments, has shut down its public infrastructure in a move suspected to be an exit scam. In early July, Abacus Market, the largest Bitcoin‑based Western darknet marketplace, abruptly went offline, triggering widespread suspicions of an exit scam. As the darknet continues to grow, its markets are expected to adopt even more sophisticated tools for secure trading, further enhancing the user experience and solidifying their role in modern commerce. One of the most notable markets is PhantomX, which has gained popularity for its robust escrow system and multi-signature wallet integration.
Top 7 Dark Web Marketplaces
Dark web operators use mainstream social media platforms to promote illicit goods. Advertisements for fake passports, stolen credit card dumps, and malware appear in private groups, often disguised with coded language. Once contact is made, vendors transition discussions to secure messaging apps to complete the transaction. Another key player is NebulaTrade, which focuses on user anonymity through advanced Tor routing and zero-knowledge proofs. This market has also introduced AI-driven vendor verification systems, ensuring that only reputable sellers are allowed to operate.
Cyble Strato Cloud Security
To outpace criminals, continuous innovation in AI-driven analytics and forensic tools is necessary, ensuring real-time monitoring and intervention. Whereas, Pyramid schemes focus on recruitment rather than legitimate products, often disguised as crypto investments. With decentralized finance (DeFi) and social media amplifying scams, investors must remain vigilant against fraudulent schemes. The rise of Ransomware-as-a-Service (RaaS) has further escalated cyber extortion, allowing criminals to execute attacks without technical expertise.
Additionally, where non-compliant cash out points are facilitating the movement of illicit funds from DNMs, regulators and law enforcement may take action to disrupt activity at the cash out point itself. For example, concurrent with the takedown of Hydra was the sanctioning of Garantex, the Moscow-based exchange that made multiple transactions with Hydra-linked addresses. The first ever DNM — called Silk Road — was started in 2011 by U.S. citizen Ross Ulbricht. While it included some innocuous listings such as health supplements, the majority of vendors and most of the sales were related to illicit drugs.
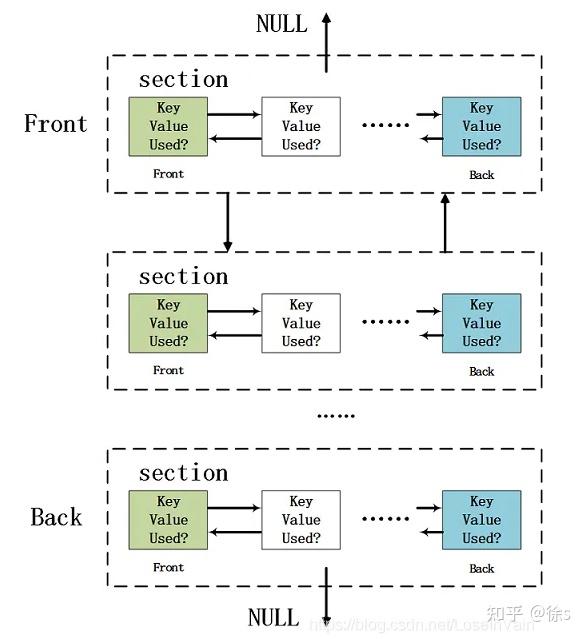
(a) Schematic representation of an ego network surrounding a dark web marketplace (“DWM”, in red). User-to-user (U2U) pairs are represented by arrows (direction indicates the flow of Bitcoin) and by their respective users. Darknet markets (DNMs) supply all manner of goods, some legal, others less so, but all purchasable with cryptocurrency and delivered to your door. Indeed, many people’s first exposure to bitcoin is when they have the need to purchase something off the darknet.
Some have implemented distributed hosting, robust compartmentalization, and enhanced privacy features to mitigate centralized points of failure. ‘Hugbunter,’ an administrator at the dark web forum called Dread, had been in contact with the team behind Abacus for a long time. TRM Labs says the site’s operators probably closed the doors and ran off with customers’ funds in a classic exit scam. Some experts still think police may have secretly seized the servers, but no agency has claimed credit for the closure yet.
These resources allow users to access verified platforms that prioritize security, anonymity, and reliability. The best darknet markets are characterized by their robust encryption protocols, transparent vendor ratings, and diverse product offerings. Previous analyses of U2U trading relationships around DWMs include only two studies21,22 based on unstructured21 or semi-structured22 interviews of 17 users of Silk Road and 13 sellers on various DWMs, respectively.

Marketplaces like Abacus Market, STYX Market, and others have evolved into well-structured hubs with user-friendly interfaces, customer review systems, and dispute resolution mechanisms. Their design mirrors legitimate e-commerce platforms, but their operations revolve around illegal products and services. At KELA, we help you identify and mitigate risks by providing actionable intelligence from the darknet. Our solutions empower you to monitor illicit darknet marketplaces and track emerging threats, ensuring you can take proactive measures to protect your organization and reputation. Darknet marketplaces emerged around 2011, with Silk Road setting the standard for how these platforms operate. Built on Tor, these sites mask IP addresses by routing traffic through encrypted relays, ensuring anonymity for both buyers and sellers.
Cryptocurrencies, especially Bitcoin and Monero, are commonly used for ransom payments due to their pseudonymity and global reach. While Bitcoin’s transparent ledger aids forensic investigations, Monero’s privacy features make tracing transactions difficult. In response, governments are enhancing blockchain surveillance and enforcing stricter regulations to combat crypto-enabled cybercrime. The prevention of these threats demands more robust regulation, better KYC/AML mechanisms, and increased blockchain analysis.
- It contains a good selection of product listings that range over 35,000 items.
- As the darknet continues to grow, its markets are expected to adopt even more sophisticated tools for secure trading, further enhancing the user experience and solidifying their role in modern commerce.
- To be classified as a seller, an entity must simultaneously satisfy the six feature threshold criteria, as follows.
- These search engines neither track your search queries nor record any information, improving digital privacy and keeping your data private.
Identifying Key Players In Dark Web Marketplaces Through Bitcoin Transaction Networks

You can even use a secure email provider or a burner email address whenever you visit the dark web. Having JavaScript enabled on the dark web can cause havoc because it can reveal your IP address to your website. Also, previously, the Tor browser was vulnerable to JavaScript attacks as it provided hackers a pathway to track your activities by using the session details.
NFTs, DeFi, And The Next Wave Of Crypto Crimes
Crypto anonymity tools, such as mixing services (tumblers) and privacy coins, enhance transaction privacy by obscuring the origin of funds. These tools pool and redistribute transactions, making it challenging to trace senders and recipients. While they provide anonymity, they also pose regulatory challenges by complicating financial tracking and raising concerns about illicit activities. Each marketplace is a star-graph where the central node is the marketplace, and the leaf nodes, i.e., the first-neighbors, are the marketplace users. Therefore, all transactions involving the market have the market either as a source or as a destination node. The horizontal bars represent each market lifetime, i.e., the time when the market becomes active until its closure, and is colored according to the market’s monthly trading volume in USD.



