
Furthermore, it’s critical to understand that Whonix is not a stand-alone browser. It is a component of Whonix, an operating system that functions as a whole inside a virtual computer. It includes all the essential productivity software, including MS Word and an email client. However, there are some significant variances in the background despite the similarities. For example, Whonix’s virtual workstation machine connects to the internal virtual LAN.
Like any other site of such nature, Awazon Market isn’t free from risks, so be careful while accessing it. Since Hidden Wiki maintains all kinds of websites, ensure you don’t open something you don’t want to see. You can choose the best darknet (.onion) website that suits you and start surfing. For safer browsing, it is highly recommended to also use a VPN and antivirus software. For businesses and individuals alike, understanding these threats is the first step in securing their digital assets.
Why Is A VPN Important When Accessing The Dark Web?
Then, use a powerful identity theft protection tool, like LifeLock Standard, to help find out if your personal data is leaked on the dark web. Market lists, often updated regularly, provide users with direct access to active onion URLs, reducing the risk of phishing or scams. These lists are curated based on user feedback, uptime, and overall reputation, making them indispensable tools for navigating the darknet landscape. Additionally, the integration of Bitcoin and other cryptocurrencies ensures seamless and private transactions, further enhancing the user experience.
Fraudulent Markets
The goods on sale range from stolen credit card data and forged documents to illegal drugs, weapons, malware as a service, and hacking tools. Platforms such as AlphaBay Reloaded and WhiteHouse Market have established themselves as leaders, leveraging advanced encryption and escrow systems to ensure safe transactions. These markets prioritize user anonymity, integrating features like multi-signature wallets and decentralized hosting to mitigate risks. Bitcoin remains the primary currency for transactions, providing a seamless and secure payment method. The integration of multi-signature wallets and escrow services further minimizes risks, ensuring that both buyers and sellers are protected throughout the transaction process. These features have significantly reduced instances of fraud, making darknet markets a reliable option for drug trade.
Dark Web Search: The Best Dark Web Search Engines In 2025
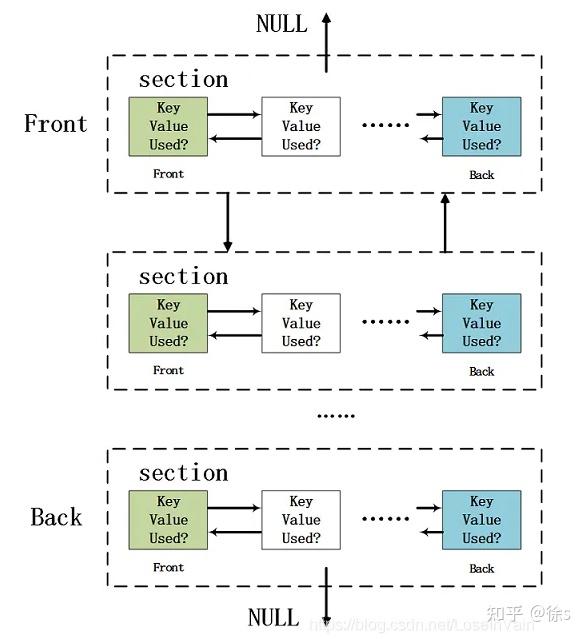
Centralized darknet markets are taking hits—think Hydra’s takedown in 2022. Now, places like ASAP are talking decentralized setups, spreading the load across nodes so they’re harder to shut down. I’ve seen some beta versions popping up on forums, and they’re rough but promising. Policing involves targeting specific activities of the private web deemed illegal or subject to internet censorship. DuckDuckGo is built into the Tor browser, making it a convenient option for looking up dark web websites.
This solution focuses on identifying stolen data, brand misuse, and potential threats before they can cause significant harm. With Brandefense, businesses gain early visibility into risks that may otherwise remain undetected until it’s too late. This trove of stolen data included names, addresses, Social Security numbers, and phone numbers, leaving millions of individuals vulnerable to identity theft. Shortly after the breach, a hacker group known as USDoD listed this data on dark web marketplaces, pricing it at a staggering $3.5 million. The very first of these marketplaces to pair the darknet with Bitcoin was the Silk Road. Over the next two years, the Silk Road set the standard for darknet marketplaces.
What Kind Of Content Is On The Dark Web?

Learn how to automate financial risk reports using AI and news data with this guide for product managers, featuring tools from Webz.io and OpenAI. Join millions of users who trust ForestVPN for privacy and unrestricted internet access. However, any illegal activities conducted on the dark web, such as purchasing illicit goods or engaging in criminal behavior, are still punishable by law. It offers outstanding privacy features and there is currently a discounted rate available through this link. The advantage of using a dedicated computer just to browse the dark web is that your main computer isn’t exposed to any of the threats or risks tied to entering the dark web. In case of an attack, you can be sure that any of the data or information stored on your main computer will be safe.
These anonymous marketplaces—operating mainly on the Tor network—are now a primary threat vector for businesses and cybersecurity professionals. The dark web also helps individuals communicate about or sell illegal items such as weapons, drugs, malware, etc. Many people see hacked information and stolen card data being sold on the dark web. For example, you can find information unavailable to the public and share data privately while protecting your online identity. Note that most dark web transactions are carried out using Bitcoin or other cryptocurrencies.
Dark Web Tools And Services
But if you are thinking you can find links to the deepest part of the dark web using this site, it’s not that simple. However, there’s no guarantee that all the links on this site are working. Some may lead to malicious sites, downloading malware on your device. The Tor browser is the most preferred browser for surfing the dark web because it creates encrypted pathways for user traffic, ensuring all the activities are anonymous. The dark web is not easily accessible, especially with browsers like Chrome or Safari, as it requires specialized protocols like Tor’s onion routing. As a result, the recommended browser for accessing the dark web is the Tor (The Onion Router) browser.
Community Forums
- The dark web, a subset of the deep web, operates on encrypted networks like Tor, requiring specialized tools for access.
- However, there’s no guarantee that all the links on this site are working.
- Therefore, use NordVPN to view search results and browse anonymously.
- So Facebook’s onion portal is a valuable tool for people living under repressive regimes.
- Platforms like SecureDrop allow these carriers of truth to evade tracking.
Law enforcement agencies monitor many dangerous markets, and even anonymous browsing isn’t foolproof. Just visiting these sites can attract attention from law enforcement, especially if you interact with known vendors or download suspicious content. Darknet marketplaces may look like regular online stores, but using or even browsing them comes with serious risks. From identity theft to law enforcement surveillance, the dangers are real — and often underestimated. Most buyers and sellers use the Tor network, which hides IP addresses and locations.
- Even if someone does try to track you, they’re going to be taken to a random part of the world where don’t exist, rather than your computer and internet address in the real world.
- In this post, we’ll walk you through the top 10 dark web marketplaces that you need to watch for potential threats to your organization.
- The editor will then create a link for you to forward to the sender.
- It has been estimated that a large percentage of dark web traffic is related to illegal pornography that includes underage victims.
- In 2025, the darknet continues to serve as a robust platform for secure and reliable drug trade, with several markets standing out due to their advanced features and user-centric designs.
The email service is available both on the surface and on the dark web. Hence, if you participate in them, whether knowingly or unknowingly, you can end up putting criminal charges on yourself, and in some extreme cases, even imprisonment. Check out these best onion sites to access the dark web securely and anonymously.

It will make your VPN activities seem like normal traffic, so you can use an uncensored internet. However, this feature is only available on iOS, Android, and Windows. ExpressVPN is an excellent choice for Tor and accessing the Dark Web. It has a proprietary onion site in the Tor network to give you safe access even if your country restricts VPN usage.
Like regular browsers with domain names, the Tor browser also has its own domain designation. These “onion” sites are only accessible on the dark web and bear the “.onion” domain at the end of the URL. This is no different from the “.net” or “.com” of the regular Internet. This is an estimated reading time to let you know how long it will take you to read all the content on this particular PrivacyRadar.com page. However, it has a sneak peek, easy guide steps, and/or a quick list providing quick in-page navigations and easily-found answers if desired. Bitcoin’s blockchain is too leaky these days, and markets like Archetyp going Monero-only prove it.
Wherever you go online, but especially if you’re on dark web websites, using a VPN helps you secure your communication data and protect personal information you send or receive. Avast SecureLine VPN encrypts all of your internet traffic to help block hackers and keep snoops out. Install Avast SecureLine VPN today to browse safely and securely, wherever your online travels take you. You can access onion sites only through the Tor browser or special network configurations. On the Tor network, the onion domain name reflects the fact that, like the layers of an onion, the Tor browser consists of layers of protection. Tor encrypts traffic, masks your IP address, blocks trackers and browser fingerprinting, and doesn’t store a record of your activity.
In the summer of 2017, a team of cyber cops from three countries successfully shut down AlphaBay, the dark web’s largest source of contraband, sending shudders throughout the network. Many dark websites are set up by scammers, who constantly move around to avoid the wrath of their victims. Even commerce sites that may have existed for a year or more can suddenly disappear if the owners decide to cash in and flee with the escrow money they’re holding on behalf of customers. Dark web search engines exist, but even the best are challenged to keep up with the constantly shifting landscape.
Keep in mind what you’re looking for, find that information, and disconnect from the dark web. As enticing as it might be, don’t follow links to other parts of the dark web. Simply download the file, install the software, and you’re ready to use its web-based interface. Opennet connections are easier to use, but darknet connections provide more security against attackers on the network. I2P can only be used to access hidden sites that are only available on the I2P network.



