
I possess a keen interest in exploring and understanding the intricacies of malware, Advanced Persistent Threats (APTs), and various cybersecurity challenges. My dedication to continuous learning fuels my passion for delving into the complexities of the cyber world. When you’re done surfing or shopping on the dark web, don’t forget to shut down Tails.
Individual sites on the dark web look much like they do on the regular web, though a lot of them are a bit more rough around the edges. (Presentation and polish isn’t quite so important on this part of the internet.) Click on any website link, and it’ll appear on screen, with its address at the top. Cybersecurity has to also cover everything physically on your computer too—which law enforcement or government authorities might have the right to seize if they come calling. If you want to be untraceable and undetectable, connecting to the dark web via the Tor browser is a major step towards that, but not the only step you’ll need. These days, it can seem increasingly difficult to protect valuable assets and data from the reaches of threat actors. This is particularly true for enterprise organizations working with sensitive data in key sectors like healthcare, energy, and finance.
Understanding The Onion Network And Accessing The Dark Web
This technology initially had noble intentions, aiming to protect activists, whistleblowers, and individuals in repressive regimes. However, it soon became a double-edged sword as malicious actors began to exploit its capabilities for illicit purposes. We may just have heard of the Dark Web if you are a curious person to seek to explore the depths of the Internet.
Privacy and security are essential concerns when surfing the dark web. It is a high danger of fraud and theft of identities on the dark web due to the prevalence of unlawful content and crimes there. A virtual private networking (Proxy server) is just a great way to hide your online identity as well as your place whilst allowing you to access the internet securely. Personal and financial information should never be exposed on the dark web either via links from unknown sources. Improve your online health by using long passwords for each account and turning on two-factor login. You can protect your privacy and security when surfing the dark web if you take the proper procedures and retain alert.
The first section deals with cybercrime and explores some of the most famous leaks, DDoS attacks, and the deployment of viruses or worms. Archetyp Market stands out for its user-friendly interface and diverse product range. Join a vibrant community of users who share their experiences and tips. Gain entry to the Archetyp Market through its secure links and mirrors.
Transactions Completed
The Dark Web contains illegal marketplaces and other risky websites, as some of the books we reviewed indicate. These marketplaces and the potentially harmful sites thrive due to the lack of regulations. However, the Dark Web also contains whistleblowers, journalists, and people who want to avoid censorship, thanks to the space’s anonymity and privacy.
Dark Web Links Are Visible Only Via Tor Browser
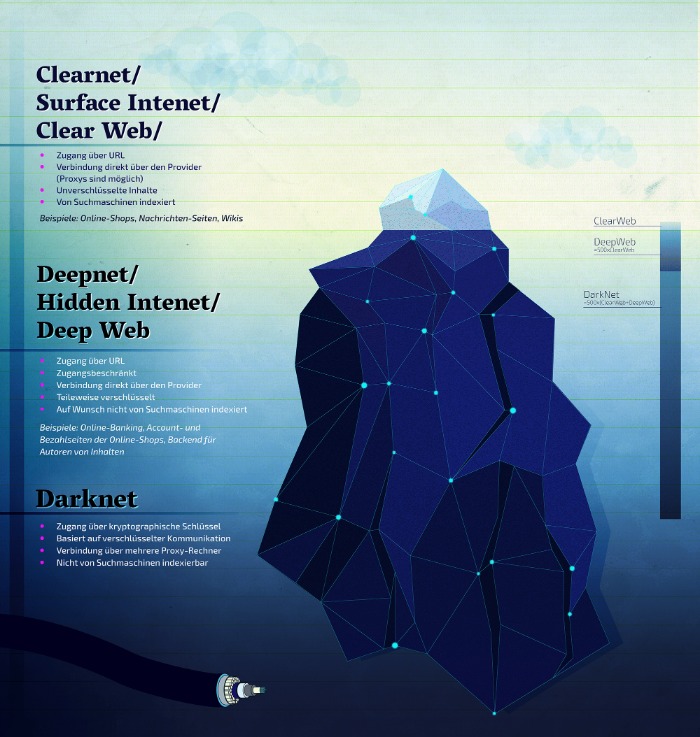
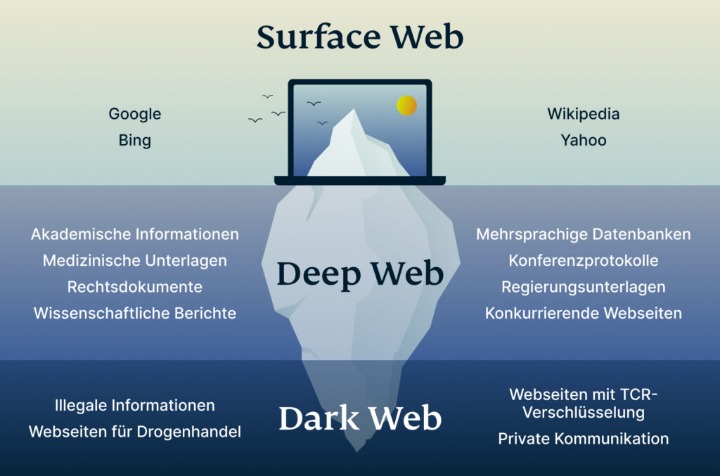
The US Supreme Court has indicated that even casual browsing could lead to legal consequences. The Dark Web is a hidden part of the internet, completely different from the clear web we all use daily. When you search for something on Google or Bing, you’re using the clear web. Identifying specific individuals who use the dark web can be quite tricky.
Cryptocurrency Transactions
- Usually dark web transactions are made with Bitcoin or other cryptocurrencies.
- Ormsby expertly told the story of the Silk Road’s rise and fall with deep insights into the world of the dark web.
- From this point onwards, you can enjoy complete anonymity and security while being able to access “.onion” websites and other dark web browser domains.
- If you’re doing very important work and you’re desperate to avoid the prying eyes of the government or any other actor, using the dark web may be worth it.
- This layer of the Internet is simple, visible, and accessible, there is nothing here that needs further explanation.
- In a world where privacy is a luxury, Archetyp Market offers you the chance to keep your transactions discreet.
Carding refers to the theft and illegal use of credit card information, and the dark web offers a platform for criminals to sell and buy such information. Talking about the fundamentals, the dark web and the darknet guarantee privacy and anonymity. Information on the dark web is not meant for public consumption, and the dark web protects personal data intended to be private. To access a dark web resource, you will need to know its web address to the letter. These websites will also use .onion top-level domain names, and many of them will be very long, random combinations of letters and numbers. You won’t be able to access .onion addresses using a standard search engine as they aren’t indexed by crawlers.
What Services And Tools Are Available On The Dark Web?
In some countries, exploring new political ideologies can be considered an imprisonable offense, and those who visit restricted websites could be placed on a watchlist or targeted for jail sentences. China, for example, uses the “Great Firewall” to restrict access to popular sites and prevent citizens from evading government restrictions. While some threats on the dark web are well-known, others may use its notorious reputation to trick users into paying large sums of money. Additionally, some users on the dark web may attempt phishing scams to steal personal information and extort victims. There are reports of illegal services on the dark web, ranging from paid assassinations to the trafficking of sex and weapons.
Swap Data In Countries That Censor The Internet
This means the VPN provider doesn’t see your real IP address and the VPN protects you from those bad exit nodes. A VPN allows a user to encrypt all internet traffic traveling to and from his or her device and route it through a server in a location of that user’s choosing. A VPN, in combination with Tor, further enhances the user’s security and anonymity.
Like I2P, Freenet is a self-contained network within the network that can’t be used to access sites on the public web. It can only be used to access the content uploaded to the Freenet, which is a peer-to-peer distributed data store. Once you upload something, it stays there indefinitely even if you stop using Freenet, so long as it is popular. After all, it’s much less popular, can’t be used to access normal websites, and isn’t as easy to use, among other disadvantages.
By integrating top-grade security into their operations, organizations can not only reduce their exposure to cyber threats but also reinforce trust in an increasingly data-driven world. As cyber threats grow more sophisticated, organizations are keeping a close watch on the dark web. Companies use dark web monitoring to scan for leaked data, stolen credentials and breach indicators, helping them track and identify perpetrators.
More On Tor Onions

You might often see news stories about criminal activity involving the dark web, and because of what’s happening in some corners of the dark web, it tends to put off law-abiding companies and users alike. Sections of the dark web are often closed down too, as part of police operations. Threat intelligence gathered from the Deep and Dark Web is likely to help future threat hunting teams when analyzing telemetry from beyond their own networks, such as the Deep and Dark Web. These differences aren’t necessarily clear-cut, as there are overlapping aspects between the Deep and Dark Web.

Guide To Navigating Darknet Search Engines
Open up Tor, and you won’t suddenly see the dark web staring back at you. Not only do you need a dark web browser, you need a dark web search engine too. This search engine will get you to the sites you need, though you can also go directly to dark web addresses if you know what they are, as with standard URLs. To get on the dark web, you need a browser built for the job, and the best in the business is Tor.
Tails never writes anything to the computer’s hard drive, running only from the RAM of the computer, which is wiped clean when the computer is shut down. The advantage of using a dedicated computer just to browse the dark web is that your main computer isn’t exposed to any of the threats or risks tied to entering the dark web. In case of an attack, you can be sure that any of the data or information stored on your main computer will be safe.
Freenet is one of the oldest anonymity networks, focused on providing censorship-resistant communication. Instead of simply routing traffic, Freenet stores encrypted chunks of data across nodes. I2P is an anonymous overlay network designed primarily for peer-to-peer applications. However, browsing the Darknet will be confusing and uneventful for first-timers. Beginners will have to resort to directories to find “Hidden Services”, which is what sites are called on the Tor Network.



