Also, only use .onion links from legitimate sources like The Hidden Wiki. It’s legal to use the dark web in most countries, but there are places where using the dark web might be against the law. I strongly advise doing your own research to make sure you’re not breaking any local laws by visiting the dark web. Also, even in countries where accessing the dark web is legal, it’s still against the law to use or host sites that promote criminal activities. It’s also a playground for cybercriminals, illegal activities, and shady stuff.
What Is The Dark Web And How To Access It?
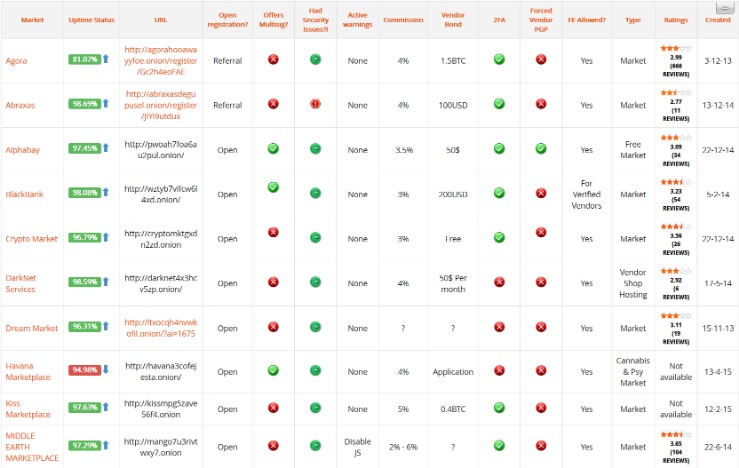
Darknet markets have undergone several transformations since their inception. From the shutdown of Silk Road in 2013 to the rise and fall of major platforms like AlphaBay and Dream Market, the ecosystem has continually adapted. Law enforcement pressure has forced these markets to evolve, with newer platforms adopting stronger security protocols, decentralized architectures, and better anonymity tools.
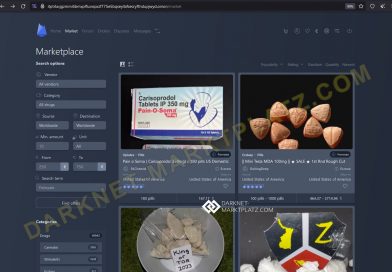
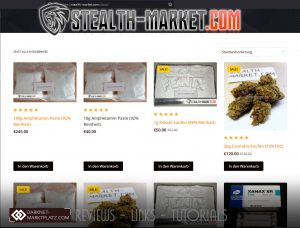
The darknet also offers a diverse range of products, catering to various preferences and needs. From pharmaceuticals to recreational substances, the availability of detailed product descriptions and lab-tested results ensures informed purchasing decisions. This level of transparency and accessibility has solidified the darknet as a reliable hub for the drug trade in 2025. The product listings on these markets are more comprehensive than ever, featuring detailed descriptions, high-quality images, and verified reviews. This transparency ensures that buyers can trust the quality and authenticity of the products they purchase. Additionally, many markets now include escrow systems and dispute resolution mechanisms, further safeguarding transactions.
Stay private with a tool like Surfshark’s Alternative ID to mask your contact details and use generated data on sites you don’t trust. Given the above threats, it’s a good idea to use Tor over a VPN to access the dark web. ZeroBin is an attractive option for anyone looking to share sensitive information without compromising privacy. It’s particularly useful for journalists, whistleblowers, and those who urgently need to send or receive confidential data. This space for private free speech also carries the risk of exposing you to harmful content.
It’s a popular choice for users worried about online surveillance and data collection. Some believe STYX is the OG darknet market when it comes to financial crimes. It trades in hacked bank accounts, stolen credit card information, and other services that facilitate cryptocurrency laundering. Every potential participant’s credentials must be vigorously vetted before they can join. That way, they aim to create secure forums and limit outsiders like law enforcement.
- For information concerning the process for seeking removal from an OFAC list, including the SDN List, please refer to OFAC’s Frequently Asked Question 897 here.
- The unique part is that the platform offers free samples of stolen information, often to attract more customers.
- The US Naval Research Laboratory developed The Onion Routing (Tor) project in the late 90s.
- You can find items like digital goods, software, and even collectibles.
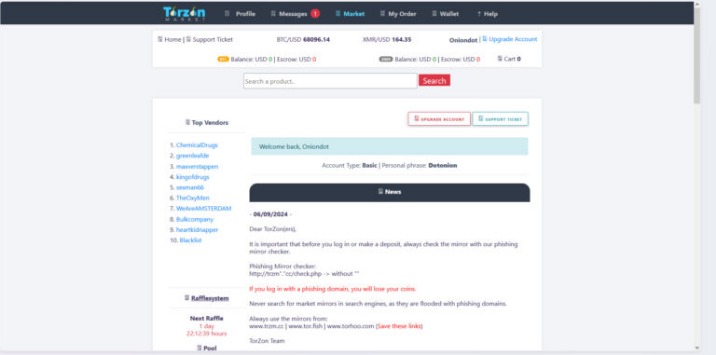
Look for ratings below 90% or no escrow—common red flags on markets like Torrez. Download Tor Browser from torproject.org—your entry to the onion network. Phoenix Nexus is reputed to have decentralized hosting servers in multiple continents, ensuring it stays operational even during targeted takedowns.
Stolen Personal Data
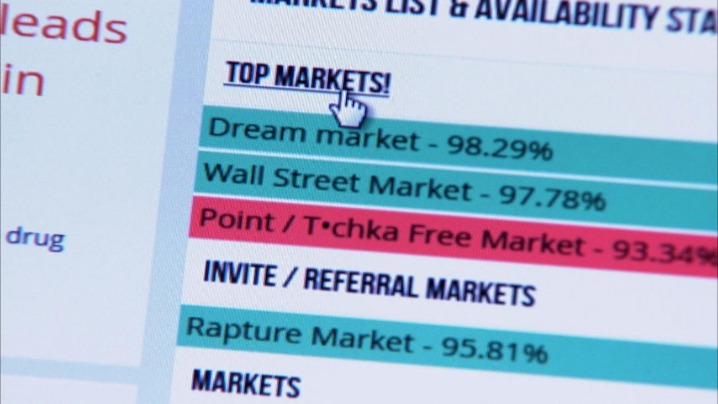
Scientific journals often put their articles behind a paywall and charge high fees for access, but Sci-Hub offers open access to read or download research papers. While it’s a deep resource, it’s also illegal in many countries, because it may violate copyright restrictions, so check out the laws in your area before visiting. Law enforcement shutdowns are also only one type of disruption that dark web communities face. In some cases, established sellers on closed-down markets are welcomed onto new markets as digital “refugees” and have joining fees waived. The durability of these markets tells us that if policing responses keep following the same playbook, they will keep getting the same results.
ProPublica — Investigative Journalism News Site
These are communities stretched across dark and surface web forums which develop shared tutorials and help one another adapt to any new changes. These closures bind users together and foster a shared resilience and collective experience in navigating these environments. These included an advanced encryption program known as “Pretty Good Privacy” and a cryptocurrency called Monero.
However, there are some significant variances in the background despite the similarities. For example, Whonix’s virtual workstation machine connects to the internal virtual LAN. It can only interact with the gateway, the most effective method by which the browser protects user applications from learning a device’s IP address. To prevent detection, the program runs user data via a tiered stream before allowing access to the dark web.
Popular Dark Web Links & Websites
Activists and government critics prefer to remain anonymous, fearing repercussions if their identities are revealed. Besides, victims of crime may want to hide their identities from their perpetrators. Nonetheless, if whatever you do is deemed illegal in your country, you can get into trouble.
The Bright Future Of Darknet Drug Trade

Therefore, you need to start by changing your passwords, and you need to notify your credit card or bank provider. The unique part is that the platform offers free samples of stolen information, often to attract more customers. Thank you for choosing Ares Link as a marketplace for the purchase of darknet goods.
Image Hosting — Upload & Share Images
The platform allows buyers to review the vendor’s products and services, so it’s easy for them to decide if the vendor is reputable or just scamming them. You can see all the product categories the marketplace deals with on the homepage. Like other marketplaces, it also requires registration for new users and accepts payments in Monero. Tor2door powers 25,000+ listings and $4.5M monthly trades via BTC and XMR, holding a 7% share. Its 13,000+ users and 1,100+ vendors rely on a secure, fast-paced trading network. Incognito channels 20,000+ listings and $2.8M monthly trades through BTC and XMR, with a 5% market presence.
The story of dark web marketplaces kicks off with Silk Road, launched in 2011. It was the first big site where people could anonymously buy drugs using Bitcoin, and it gained a lot of attention, until it was shut down by the FBI in 2013. Keybase is a secure platform that lets people chat, share files, and collaborate — kind of like a privacy-first version of cloud storage service Dropbox or communication platform Slack.
Accessing blocked content can result in being placed on a watch list or imprisonment. Remember that illegal activities can still incriminate you, whether you are using a Tor browser. For example, you shouldn’t pirate copyrighted material, engage in terrorism, or share illegal pornography. The creators assert that because their technique is so strong, even malware with root access could not determine the machine’s IP address. No user names are tied to actual identities, and no moderation like one may find on Reddit.
Following the closure of AlphaBay, the abacus market has emerged as a significant player in the evolving landscape of darknet markets, facilitating illegal trade and cybercrime. Freshtools is a unique marketplace in that it does not only provide the stolen data, but it allows criminals to purchase MaaS which can cause further damage to the victims. It is one of the most active and up to date markets and always provides new and updated malware and data. All resources are offered to give insight into the workings of the Tor network and darknet markets. Use at your own discretion and always remain within the laws of your jurisdiction.
If you ever decide to explore the dark web, protecting your identity is crucial. Most people start by using the Tor Browser, which hides your IP address. It’s been a constant back-and-forth between cybercriminals and law enforcement, with each new site trying to be smarter and more secure than the last. These sites cater to cybercriminals seeking valuable data, such as credit card numbers, login credentials, and personal information. The second category consists of data stores, which specialize in stolen information.



